Navigating server-side development requires meticulous planning, encompassing routing, authentication, and data handling—a checklist ensures a robust and secure foundation for your web applications.
What is Server-Side Programming?
Server-side programming fundamentally concerns the logic that powers web applications behind the scenes. Unlike client-side code, which executes within a user’s browser, server-side code runs on a remote server. This server processes requests from clients (like web browsers), interacts with databases, and delivers dynamic content.
Essentially, when you submit a form – such as a user registration – the data isn’t directly processed in your browser. Instead, it’s sent to the server where server-side code handles the information, potentially storing it in a database. This process involves creating objects, like a ‘redditUser’ object, and managing data securely.
It’s the engine that handles HTTP requests, manages user authentication, and ensures the application functions correctly. Understanding this distinction is crucial for full-stack development, bridging the gap between what the user sees and how the application operates.
The Role of Back-End Code
Back-end code is the core of any dynamic web application, responsible for processing data, managing logic, and ensuring seamless functionality. It’s where routing directs requests to the appropriate server-side logic, handling everything from user authentication to database interactions. This code doesn’t directly interact with the user interface; instead, it prepares and delivers data to the front-end for display.

Historically, developers might focus solely on client-side work, but increasingly, understanding back-end principles is vital. Building an HTTP server, for example, requires direct engagement with requests and responses. Frameworks like Express, Koa.js, and Hapi.js simplify this process, offering structure and tools for efficient development.
Ultimately, the back-end ensures data integrity, security, and scalability, forming the invisible yet essential foundation of the web experience.

Setting Up Your Server Environment
Establishing a solid server environment involves selecting a language like Node.js, choosing a framework (Express, Koa.js, or Hapi.js), and integrating databases effectively.
Choosing a Server-Side Language (Node.js Focus)
Selecting the right server-side language is paramount, and Node.js has emerged as a popular choice for modern web development. Its JavaScript runtime allows developers to utilize a single language across both the front-end and back-end, streamlining the development process and fostering code reusability. Node.js’s non-blocking, event-driven architecture makes it exceptionally well-suited for building scalable and real-time applications.
Compared to traditional server-side languages, Node.js often boasts faster development cycles and improved performance, particularly for I/O-bound operations. The extensive npm package manager provides access to a vast ecosystem of libraries and tools, accelerating development and simplifying complex tasks. However, it’s crucial to consider the single-threaded nature of Node.js and implement appropriate strategies for handling CPU-intensive operations to prevent blocking the event loop. Ultimately, Node.js offers a compelling blend of performance, scalability, and developer productivity, making it a strong contender for many server-side projects.
Selecting a Web Framework (Express, Koa.js, Hapi.js)
Once Node.js is chosen, selecting a web framework becomes crucial for structuring your server-side application. Express.js, a minimalist framework, offers flexibility and a large community, making it ideal for rapid prototyping and smaller projects. Koa.js, designed by the same team as Express, emphasizes modern JavaScript features like async/await, resulting in cleaner and more readable code. It aims to be a more expressive and robust foundation for web applications and APIs.
Hapi.js, on the other hand, prioritizes configuration over convention, providing a highly structured and scalable environment, particularly suited for complex applications and microservices. Each framework presents a different approach to routing, middleware, and request handling. The best choice depends on project requirements, team familiarity, and desired level of control. Evaluating these factors ensures a framework aligns with your development goals and promotes maintainability.
Database Integration Considerations
Integrating a database is fundamental to most server-side applications, requiring careful consideration of several factors. Choosing the right database – relational (like PostgreSQL or MySQL) or NoSQL (like MongoDB) – depends on your data structure and application needs. Relational databases excel with structured data and complex relationships, while NoSQL databases offer flexibility and scalability for unstructured data.
Connection pooling is vital for efficient database access, minimizing overhead and improving performance. Data modeling should align with application requirements, ensuring data integrity and efficient querying. Security is paramount; employ parameterized queries to prevent SQL injection vulnerabilities. Consider Object-Relational Mapping (ORM) tools to simplify database interactions and abstract away database-specific details, enhancing code maintainability and portability.

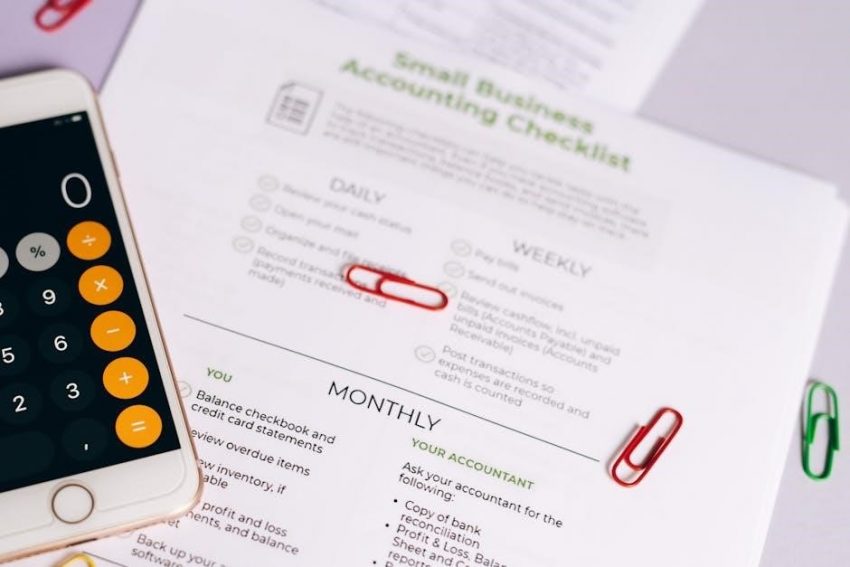
Core Server-Side Tasks Checklist
Essential tasks include routing requests, handling user authentication, validating data, and implementing CRUD operations for seamless database interactions and application functionality.
Implementing Routing and Request Handling
Routing is fundamental to server-side development, dictating how your application responds to different client requests. A comprehensive checklist begins with defining clear URL paths and associating them with specific server-side logic. This involves meticulously mapping HTTP methods (GET, POST, PUT, DELETE) to corresponding handler functions.

Ensure each route accurately processes incoming data, validating its format and content before proceeding. Implement robust error handling to gracefully manage invalid requests or unexpected issues. Consider using middleware to streamline common tasks like authentication or logging.
Furthermore, prioritize code organization by grouping related routes into modules or controllers. Thoroughly test each route with various inputs to guarantee predictable and reliable behavior. Proper request handling is crucial for a responsive and user-friendly web application.
User Authentication and Authorization
Securely managing user access is paramount, beginning with robust authentication mechanisms. A checklist should prioritize verifying user credentials – usernames and passwords – against a secure database. Implement strong password hashing algorithms like bcrypt to protect sensitive information. Consider multi-factor authentication for enhanced security.
Once authenticated, authorization determines what resources a user can access. Define clear roles and permissions, granting access based on user identity. Utilize techniques like JSON Web Tokens (JWT) or OAuth for secure authorization.
Regularly review and update access controls to reflect changing user roles. Implement proper session management to prevent unauthorized access. Thoroughly test authentication and authorization flows to identify and address potential vulnerabilities.
Data Validation and Sanitization
Protecting your application from malicious input is crucial; a checklist must include rigorous data validation and sanitization procedures. Validate all user-supplied data – forms, API requests, and query parameters – against expected formats and constraints. Implement both client-side and server-side validation, but always trust server-side validation as the definitive check.
Sanitize data to remove or encode potentially harmful characters, preventing vulnerabilities like cross-site scripting (XSS) and SQL injection. Utilize appropriate encoding functions for different data types.
Regularly update validation rules to address emerging threats. Implement whitelisting approaches, allowing only known-good input. Thoroughly test validation and sanitization routines to ensure effectiveness and prevent unexpected behavior.
Database Interactions (CRUD Operations)
Efficient and secure database interactions are fundamental; your checklist should detail the implementation of CRUD (Create, Read, Update, Delete) operations. Define clear data models and schemas to ensure data integrity. Utilize parameterized queries or prepared statements to prevent SQL injection vulnerabilities – a critical security measure.
Implement robust error handling for database operations, logging failures for debugging and monitoring. Optimize queries for performance, utilizing indexes and appropriate data types. Consider connection pooling to reduce database overhead.
Regularly back up your database to prevent data loss. Document all database interactions and schema changes. Ensure proper authorization controls are in place to restrict access to sensitive data.
Security Considerations Checklist
Prioritize robust security measures, including secure authentication via JWT or OAuth, and diligent protection against prevalent web vulnerabilities like SQL injection and XSS.
Secure User Authentication (JWT, OAuth)
Implementing secure user authentication is paramount for protecting sensitive data and ensuring a trustworthy application. JSON Web Tokens (JWT) offer a stateless method for securely transmitting information between parties as a JSON object, verifying user identity without repeated database queries. OAuth, on the other hand, provides delegated access, allowing users to grant third-party applications limited access to their resources without sharing their credentials directly.
When choosing between JWT and OAuth, consider your application’s specific needs. JWT is ideal for scenarios where you control both the client and server, while OAuth excels in situations involving third-party integrations. Regardless of the chosen method, always employ strong cryptographic algorithms and regularly rotate secrets to mitigate potential security risks. Proper implementation includes validating token signatures, handling token expiration, and protecting against replay attacks. Thorough testing and adherence to security best practices are crucial for a robust authentication system.
Protection Against Common Web Vulnerabilities (SQL Injection, XSS)
Safeguarding your server-side application against prevalent web vulnerabilities is non-negotiable for maintaining data integrity and user trust. SQL Injection, a critical threat, occurs when malicious SQL code is inserted into input fields, potentially granting unauthorized database access. Mitigation involves utilizing parameterized queries or Object-Relational Mappers (ORMs) to sanitize user input effectively.
Cross-Site Scripting (XSS) attacks inject malicious scripts into websites viewed by other users. Prevention requires rigorous input validation and output encoding, ensuring that user-supplied data is treated as text, not executable code. Employing Content Security Policy (CSP) further restricts the sources from which the browser can load resources. Regularly updating server-side libraries and frameworks is also vital, as updates often include patches for newly discovered vulnerabilities. Consistent security audits and penetration testing are recommended to proactively identify and address potential weaknesses.
HTTPS Implementation and SSL Certificates
Securing communication between your server and clients with HTTPS is paramount for protecting sensitive data in transit. This involves obtaining and installing an SSL/TLS certificate from a trusted Certificate Authority (CA). The certificate verifies your server’s identity and encrypts data using TLS protocols, preventing eavesdropping and man-in-the-middle attacks.
Configuration typically involves updating your web server (e.g., Apache, Nginx) to listen on port 443 and configuring it to use the SSL certificate and key. Regularly renewing your SSL certificate is crucial, as they expire after a certain period. Implementing HTTP Strict Transport Security (HSTS) forces browsers to always connect via HTTPS, enhancing security. Automated certificate management tools, like Let’s Encrypt, simplify the process of obtaining and renewing certificates. Thoroughly testing HTTPS configuration ensures proper functionality and avoids mixed content warnings.

Deployment and Monitoring Checklist
Successful deployment demands careful server configuration, robust logging, and proactive performance monitoring—essential for identifying and resolving issues swiftly and efficiently.
Server Configuration and Deployment
Prior to deployment, meticulously configure your server environment, ensuring optimal settings for performance and security. This includes selecting the appropriate operating system, web server (like Nginx or Apache), and necessary software dependencies. Implement a robust version control system, such as Git, to track changes and facilitate rollbacks if needed.
Automate the deployment process using tools like Docker and Kubernetes for consistency and scalability. Thoroughly test the deployment pipeline in a staging environment before pushing to production. Configure firewalls and security groups to restrict access to essential ports only. Regularly update server software to patch vulnerabilities.
Establish a clear rollback strategy in case of deployment failures. Monitor server resource utilization (CPU, memory, disk space) to identify potential bottlenecks. Document all configuration steps for reproducibility and troubleshooting.
Logging and Error Handling
Implement comprehensive logging throughout your server-side application to capture crucial information about requests, responses, and errors. Utilize structured logging formats (like JSON) for easier analysis and querying. Centralize log storage using tools like Elasticsearch, Logstash, and Kibana (ELK stack) or Splunk for efficient monitoring and troubleshooting.

Establish a robust error handling mechanism to gracefully handle exceptions and prevent application crashes. Implement global error handlers to catch unhandled exceptions and provide informative error messages. Log all errors with sufficient context, including timestamps, request details, and stack traces.
Monitor error rates and patterns to proactively identify and address potential issues. Implement alerting mechanisms to notify developers of critical errors in real-time. Consider using a dedicated error tracking service like Sentry or Rollbar.
Performance Monitoring and Optimization
Establish baseline performance metrics for key server-side operations, including request latency, throughput, and resource utilization. Utilize monitoring tools like Prometheus, Grafana, or New Relic to track these metrics over time and identify performance bottlenecks. Regularly profile your code to pinpoint areas for optimization.
Optimize database queries to reduce response times and improve overall performance. Implement caching mechanisms (e.g., Redis, Memcached) to store frequently accessed data and reduce database load. Consider using a Content Delivery Network (CDN) to cache static assets closer to users.
Regularly review and optimize your code for efficiency, minimizing resource consumption and improving scalability. Implement load testing to simulate real-world traffic and identify potential performance issues under stress.

Documentation and Testing Checklist
Comprehensive API documentation, utilizing tools like Swagger, alongside rigorous unit and integration tests, are crucial for maintainability and collaborative development efforts.

API Documentation (Swagger/OpenAPI)
Detailed API documentation is paramount for successful server-side development and collaboration. Utilizing tools like Swagger and OpenAPI allows for the creation of interactive and machine-readable documentation, significantly streamlining the integration process for front-end developers and third-party consumers. This documentation should clearly outline each endpoint, including request parameters, expected responses, and potential error codes.
Furthermore, well-maintained documentation facilitates easier debugging and reduces the learning curve for new team members. Swagger/OpenAPI enables automated testing of API endpoints, ensuring consistency and reliability. Regularly updating the documentation alongside code changes is essential to prevent discrepancies and maintain accuracy. Consider including example requests and responses to illustrate usage and expected behavior, enhancing clarity and usability for all stakeholders involved in the project lifecycle.
Unit and Integration Testing
Rigorous testing is crucial for ensuring the stability and reliability of server-side applications. Unit tests focus on verifying the functionality of individual components in isolation, while integration tests validate the interactions between different modules. A comprehensive testing strategy should encompass both approaches, covering critical business logic, data access layers, and API endpoints.
Automated testing frameworks streamline the testing process and enable continuous integration. Regularly running tests helps identify and address bugs early in the development cycle, reducing the risk of costly errors in production. Aim for high test coverage to maximize confidence in the codebase. Documenting test cases and results provides valuable insights for future development and maintenance efforts, fostering a culture of quality and accountability within the team.